Spanning Tree Protocol
Spanning Tree Protocol (STP) 802.1d is used to prevent loops within a switch network. STP uses Spanning Tree Algorithm (STA) to prevent loops ensuring stable network topology (also called convergence, where all the switches in the network converge to a known network topology). The following are the important features of STP:
STP is a layer 2 protocol that runs on switches and bridges. The purpose of STP is to remove switching loops.
All switches participating in STP exchange info with other switches in the network through messages known as BPDUs.
STP port states are Blocked, Listen, Learn, Forward, Disabled
STP Port States:
As mentioned, the purpose of STP is to prevent switching loops throughout a LAN. It is done by controlling the redundant links that connect into the same network segment. Each network segment is only allowed to have a single designated port that is used to forward traffic onto it. All other access points into the same segment are enabled, but in a blocking state that disallows traffic flow. If a failure should occur on the forwarding port, one of the blocking ports will be transitioned into forwarding state to continue to allow access to the network segment. This transition process includes a number of different states, including each of the states shown in the figure below:
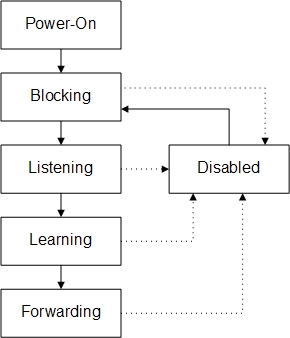
Blocking : A port that would cause a switching loop if it were active. No user data is sent or received over a blocking port, but it may go into forwarding mode if the other port in use fail and the spanning tree algorithm determines the port may transition to the forwarding state. BPDU data is still received in blocking state. Prevents the use of looped paths.
Listening : The switch processes BPDUs and awaits possible new information that would cause it to return to the blocking state. It does not populate the MAC address table and it does not forward frames.
Learning : While the port does not yet forward frames it does learn source addresses from frames received and adds them to the filtering database (switching database). It populates the MAC Address table, but does not forward frames.
Forwarding : A port receiving and sending data, normal operation. STP still monitors incoming BPDUs that would indicate it should return to the blocking state to prevent a loop.
Disabled : Not strictly part of STP, a network administrator can manually disable a port
Different port designations are given below:
Root : A bridge can have only one root port. The root port is the port that leads to the root bridge. All bridges except the root bridge will have a root port. the root port is in the STP forwarding state.
Designated : One designated port is elected per link (segment). The designated port is the port closest to the root bridge. Each designated port is in the STP forwarding state
Alternate : Alternate ports lead to the root bridge, but are not root ports. The alternate ports maintain the STP blocking state.
Backup: This is a special case when two or more ports of the same bridge (switch) are connected together, directly or through shared media. In this case, one port is designated, and the remaining ports block. The role for this port is backup.
VLAN – Virtual Local Area Networks:
VLAN derives it's name from the fact that there is only one physical network, but two or more logical networks. A VLAN may be created by any of these methods:
VLAN by port association - Membership in a VLAN can be defined based on the ports that belong to the VLAN. For example, in a bridge with four ports, ports 1, 2, and 4 belong to VLAN 1 and port 3 belongs to VLAN 2. The main disadvantage of this method is that it does not allow for user mobility. If a user moves to a different location away from the assigned bridge, the network manager must reconfigure the VLAN.
VLAN by MAC address association: Here, membership in a VLAN is based on the MAC address of the workstation. The switch tracks the MAC addresses which belong to each VLAN (see Figure4). Since MAC addresses form a part of the workstation's network interface card, when a workstation is moved, no reconfiguration is needed to allow the workstation to remain in the same VLAN. This is unlike Layer 1 VLAN's where membership tables must be reconfigured. The main problem with this method is that VLAN membership must be assigned initially. In networks with thousands of users, this is no easy task. Also, in environments where notebook PC's are used, the MAC address is associated with the docking station and not with the notebook PC. Consequently, when a notebook PC is moved to a different docking station, its VLAN membership must be reconfigured.
VLANs by Protocol Type - VLAN membership for Layer 2 VLAN's can also be based on the protocol type field found in the Layer 2 header. For example, VLANs that carry only IP traffic and those that carry only IPX traffic. However this type of VLANs are not popular.
VLANs by IP subnet address - Membership is based on the Layer 3 header. The network IP subnet address can be used to classify VLAN membership. Although VLAN membership is based on Layer 3 information, this has nothing to do with network routing and should not be confused with router functions. In this method, IP addresses are used only as a mapping to determine membership in VLAN's. No other processing of IP addresses is done. In Layer 3 VLAN's, users can move their workstations without reconfiguring their network addresses. The only problem is that it generally takes longer to forward packets using Layer 3 information than using MAC addresses. This is the most widely used VLAN type.
Copyright © Anand Software and Training Private Limited.